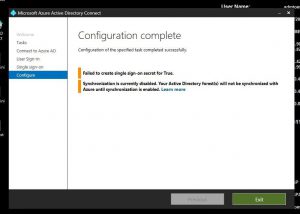
I hit this problem while working with Azure AD Connect at a customer earlier this week. The situation was that AAD Connect had already been configured with Pass-Through Authentication, which was working as expected. The next step was to enable Seamless Single Sign-On, but this failed with the following: ‘Failed to create single sign-on secret for True’.
The trace log file showed this:
[ 18] [ERROR] EnableDesktopSsoTask: Failed to create desktopsso secret for myadds.org. Exception message: System.Management.Automation.CmdletInvocationException: Exception has been thrown by the target of an invocation. —> System.Reflection.TargetInvocationException: Exception has been thrown by the target of an invocation. —> System.Runtime.InteropServices.COMException: The RPC server is unavailable. (Exception from HRESULT: 0x800706BA)
I immediately thought this was probably an issue with the firewall between the server running AAD Connect and the on-premises AD Domain Controllers. The difficulty I had was that my customer’s environment was really locked down and I didn’t have access to the firewall or to the tools I would normally use to troubleshoot something like this. So, basically I decided to try and reproduce it with my own Azure AD environment.
As expected, the problem came down to a missing firewall port (TCP 445). This port is (as of 3rd August 2017) not listed in the port requirements on this web site (Table 1):
https://docs.microsoft.com/en-us/azure/active-directory/connect/active-directory-aadconnect-ports
In my first test, I configured the firewall rules a per Table 1, i.e. without port 445 and attempted to enable SSO via AAD Connect. I received the same ‘The RPC server is unavailable’ error.
I then removed SSO manually using the Powershell method.
In my second test, I tried to enable SSO using the Powershell method. Again, I see the RPC error.
Looking at the firewall logs, I see a failed connection attempt to the ADDS DC on port 445.
2017-08-02 13:09:47 DROP TCP 192.168.237.130 192.168.237.101 50423 445 0 – 0 0 0 – – – SEND
After adding port 445 to the allowed firewall ports, I re-attempted disabling + enabling SSO using the Powershell method. This time the cmdlet completes successfully.
The status now looked good and confirms that the missing firewall rule allowing traffic from the AAD Connect server to the DCs on port 445 (TCP) was the culprit.
Interestingly, it looks like I would have hit the missing TCP 445 problem when enabling Pass-Through Authentication (i.e. prior to enabling Seamless SSO), but for the fact that I chose to use an existing AD Forest Account. If I had tried to let the Wizard create the account required for PTA it would also have failed due to TCP 445 not being available.
Hopefully this should give you enough to go on if you come across a similar issue.




Seamless SSO port requirement has now by been added by Swaroop to https://docs.microsoft.com/en-us/azure/active-directory/connect/active-directory-aadconnect-ports
Pingback: What's new in Identity? September 2017 - Identity And Access